Blog
Ransomware & Cybersecurity Predictions
Apr 17, 2026

Ransomware is evolving in technology trends for 2026, with AI-driven threats reshaping cybersecurity trends and strategies to strengthen enterprise defense and resilience.
Read MoreIT Maintenance Checklist: 7 Essential Monthly Checks
Mar 19, 2026

A structured IT maintenance checklist acts as a disciplined approach to keeping software/hardware and security defenses in top condition.
Read MoreShould Singapore SMEs invest in cyber insurance
Feb 12, 2026

As cyber risks grow more frequent and complex, investing in strong cybersecurity and cyber insurance is a practical safeguard for continuity, trust, risk management, and long-term resilience.
Read MoreThe Future of IT Outsourcing in Singapore: What Clients Expect in 2026
Jan 14, 2026

IT outsourcing in Singapore is shifting toward proactive and value-focused technology partnerships.
Read MoreA Singapore Guide to Sustainable Electronics
Nov 14, 2025

As tech consumers, it is our responsibility to play a supportive role in national sustainability goals through our daily choices and behaviors.
Read MoreWhat An Effective Data Backup Solution Looks Like
Oct 21, 2025

An effective backup solution balances data backup frequency, automation, and security to protect your data, prevent data loss, and support scalable enterprise backup strategies.
Read MoreWhy is IHP Important
Sep 15, 2025
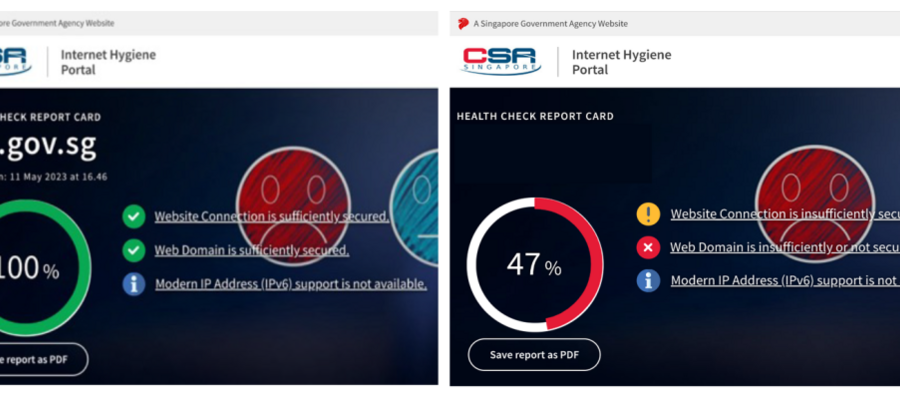
The Internet Hygiene Portal (IHP) launched by CSA, provides a one-stop, simplified platform for enterprises to check and improve their internet security.
Read MoreWhy Businesses Need Proactive IT Management
Aug 13, 2025

Proactive IT Management with system monitoring ensures a reduction in downtime and disruption of business operations and boosts productivity and business growth.
Read More